当前位置:首页 → 计算机类 → 软件水平考试 → 中级信息系统管理工程师->某电子商务公司拟构建一个高效、低成本、符合公司实际业务发展需
某电子商务公司拟构建一个高效、低成本、符合公司实际业务发展需求的OA(Office Automation)系统。张工主要承担了该系统的文档管理和通知管理模块的研发工作。文档管理模块的主要功能包括添加、修改、删除和查看文档。通知管理模块的主要功能是通知群发。
张工通过前期调研和需求分析进行了概念模型设计,具体情况分述如下:
【需求分析结果】
(1)该公司设有财务部、销售部、广告部等多个部门,每个部门只有一名部门经理,有多名员工,每名员工只属于一个部门。部门信息包括:部门号、名称、部门经理和电话,其中部门号唯一确定部门关系的每一个元组。
(2)员工信息包括:员工号、姓名、岗位号、部门号、电话、家庭住址。员工号唯一确定员工关系的每一个元组;岗位主要有经理、部门经理、管理员等,不同岗位具有不同的权限。一名员工只对应一个岗位,但一个岗位可对应多名员工。
(3)通知信息包括:编号、内容、通知类型、接收人、接收时间、发送时间和发送人。其中(编号,接收人)唯一标识通知关系中的每一个元组。一条通知可以发送给多个接收人,一个接收人可以接收多条通知。
(4)文档信息包括:编号、文档名、标题、内容、发布部门、发布时间。其中编号唯一确定文档关系的每一个元组。一份文档对应一个发布部门,但一个部门可以发布多份文档;一份文档可以被多名员工阅读,一名员工可以阅读多份文档。另外,公司为了掌握员工对文档的阅读及执行情况,还要求记录每个员工对同一篇文档分别在哪些时间阅读过。
【概念模型设计】
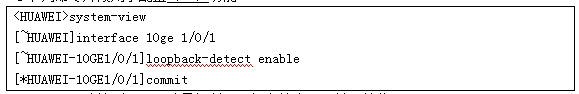
根据需求分析阶段收集的信息,设计的实体联系图(不完整)如图1-1所示:
【逻辑结构设计】
根据概念模型设计阶段完成的实体联系图,得出如下关系模式(不完整):
部门(部门号,名称,部门经理,电话)
员工(员工号,姓名,岗位号,(a),电话)
岗位(岗位号,岗位名称,权限)
通知(编号,(b),通知类型,接收时间,(c),发送时间,发送人)
文档(编号,文档名,标题,内容,发布部门,发布时间)
阅读文档(文档编号,(d),阅读时间)
【问题1】(4分)
根据题意,将关系模式中的空(a)—(d)的属性补充完整,并填入答题纸对应的位置上。
【问题2】(4分)
根据需求分析,可以得出图1-1所示的实体联系图中联系的类型。请按以下描述确定联系类型并填入答题纸对应的位置上。
部门与员工之间的“隶属”联系类型为(e);
部门与文档之间的“发布”联系类型为(f);
员工与文档之间的“阅读”联系类型为(g);
员工与岗位之间的“对应”联系类型为(h)。
【问题3】(5分)
1)员工关系的主键为(i),员工关系的外键为(j)、(k)。
2)员工关系的外键(j)应参照(1),外键(k)应参照(m)。
【问题4】(2分)
阅读文档的主键为(文档号、员工号)的说法正确吗?为什么?
【问题1】
(a)部门号、家庭地址;
(b)内容;
(c)接收人;
(d)员工号。
【问题2】
(e)1:*
(f)1:*
(g)*:*
(h)*:1
【问题3】
(i)员工号;
(j)岗位号;
(k)部门号。(注:j、k可以互换)
(l)岗位关系岗位号;
(m)部门关系的部门号。
【问题4】
不正确。
理由:依据题干中文档信息中,“一份文档可以被多名员工阅读,一名员工可以阅读多份文档”,可以得出文档和员工实体集之间的联系类型为*:*,多对多的联系转换关系应该增加两端的码,和自身的属性,其码为两端实体集码的组合,即文档编号、员工号。但题干中要求记录一名员工对同一份文件的多次阅读,因此需要再增加阅读时间属性才能唯一标识每一个元组,所以该关系的主键应该为:(文档编号,员工号,阅读时间)
【问题1】
依据题干中员工信息,(a)处应为:部门号、家庭地址;
依据题干中通知信息,(b)处应为:内容,(c)处应为:接收人;
依据题干中文档信息中,“一份文档可以被多名员工阅读,一名员工可以阅读多份文档”,可以得出文档和员工实体集之间的联系类型为*:*,多对多的联系转换关系应该增加两端的码,和自身的属性,因此(d)处应为:员工号。
【问题2】
依据题干中“每个部门只有一名部门经理,有多名员工,每名员工只属于一个部门”可以得出部门与员工之间为1:*
依据题干中“一份文档对应一个发布部门,但一个部门可以发布多份文档”可以得出部门与文档之间为:1:*
据题干中“一份文档可以被多名员工阅读,一名员工可以阅读多份文档”,可以得出文档和员工实体集之间的联系类型为*:*
依据题干中“一名员工只对应一个岗位,但一个岗位可以对应多名员工”,可以得出员工与岗位之间的联系为:*:1
【问题3】
依据题干员工信息的描述,员工关系主键为员工号;依据员工信息、部门信息的描述结合逻辑设计的关系,员工关系的外键为:岗位号(参照岗位关系中的岗位号)、部门号(参照部门关系中的部门号)。
【问题4】
依据题干中文档信息中,“一份文档可以被多名员工阅读,一名员工可以阅读多份文档”,可以得出文档和员工实体集之间的联系类型为*:*,多对多的联系转换关系应该增加两端的码,和自身的属性,其码为两端实体集码的组合,即文档编号、员工号。但题干中“公司为了掌握员工对文档的阅读及执行情况,还要求记录每个员工对同一篇文档分别在哪些时间阅读过。”要求记录一名员工对同一份文件的多次阅读,因此需要再增加阅读时间属性才能唯一标识每一个元组,所以该关系的主键应该为:(文档编号,员工号,阅读时间)
Data security is the practice of protecting digital information from ( )access,corruption,or theft throughout its entire lifecycle. It is a concept that encompasses every aspect of information security from the ( )security of hardware and storage devices to administrative and access controls,as well as the logical security of software applications. It also includes organizational ( )and procedures.Data security involves deploying tools and technologies that enhance the organization's visibility into where its critical data resides and how it is used. These tools and technologies should ( )the growing challenges inherent in securing today's complex distributed,hybrid,and/or multicloud computing environments.Ideally,these tools should be able to apply protections like (作答此空),data masking,and redaction of sensitive files, and should automate reporting to streamline audits and adhering to regulatory requirements.
Data security is the practice of protecting digital information from ( )access,corruption,or theft throughout its entire lifecycle. It is a concept that encompasses every aspect of information security from the ( )security of hardware and storage devices to administrative and access controls,as well as the logical security of software applications. It also includes organizational ( )and procedures.Data security involves deploying tools and technologies that enhance the organization's visibility into where its critical data resides and how it is used. These tools and technologies should (作答此空)the growing challenges inherent in securing today's complex distributed,hybrid,and/or multicloud computing environments.Ideally,these tools should be able to apply protections like ( ),data masking,and redaction of sensitive files, and should automate reporting to streamline audits and adhering to regulatory requirements.
Data security is the practice of protecting digital information from ( )access,corruption,or theft throughout its entire lifecycle. It is a concept that encompasses every aspect of information security from the ( )security of hardware and storage devices to administrative and access controls,as well as the logical security of software applications. It also includes organizational (作答此空)and procedures.Data security involves deploying tools and technologies that enhance the organization's visibility into where its critical data resides and how it is used. These tools and technologies should ( )the growing challenges inherent in securing today's complex distributed,hybrid,and/or multicloud computing environments.Ideally,these tools should be able to apply protections like ( ),data masking,and redaction of sensitive files, and should automate reporting to streamline audits and adhering to regulatory requirements.
Data security is the practice of protecting digital information from ( )access,corruption,or theft throughout its entire lifecycle. It is a concept that encompasses every aspect of information security from the (作答此空)security of hardware and storage devices to administrative and access controls,as well as the logical security of software applications. It also includes organizational ( )and procedures.Data security involves deploying tools and technologies that enhance the organization's visibility into where its critical data resides and how it is used. These tools and technologies should ( )the growing challenges inherent in securing today's complex distributed,hybrid,and/or multicloud computing environments.Ideally,these tools should be able to apply protections like ( ),data masking,and redaction of sensitive files, and should automate reporting to streamline audits and adhering to regulatory requirements.
Data security is the practice of protecting digital information from (作答此空)access,corruption,or theft throughout its entire lifecycle. It is a concept that encompasses every aspect of information security from the ( )security of hardware and storage devices to administrative and access controls,as well as the logical security of software applications. It also includes organizational ( )and procedures.Data security involves deploying tools and technologies that enhance the organization's visibility into where its critical data resides and how it is used. These tools and technologies should ( )the growing challenges inherent in securing today's complex distributed,hybrid,and/or multicloud computing environments.Ideally,these tools should be able to apply protections like ( ),data masking,and redaction of sensitive files, and should automate reporting to streamline audits and adhering to regulatory requirements.
以下关于项目风险管理的说法中,不正确的是( )。
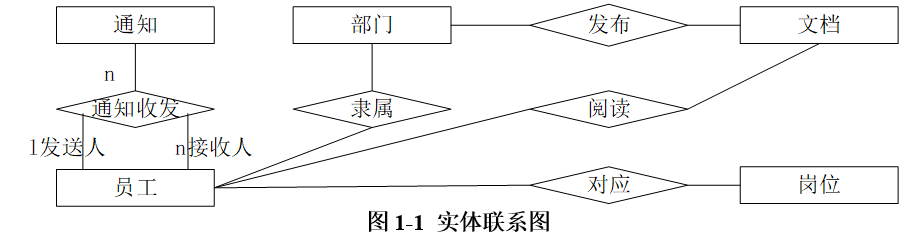
某分公司财务 PC 通过专网与总部财务系统连接,拓扑如图8所示。某天,财务PC访问总部财务系统速度缓慢、时断时好,网络管理员在财务PC端ping总部财务系统,发现有网络丢包,在光电转换器1处ping总部财务系统网络丢包症状同上,在专网接入终端处ping 总部财务系统,网络延时正常无丢包,光纤1两端测得光衰为-28dBm,光电转换器1和2指示灯绿色闪烁。 初步判断该故障原因可能是( ),可采用(作答此空)措施较为合理。
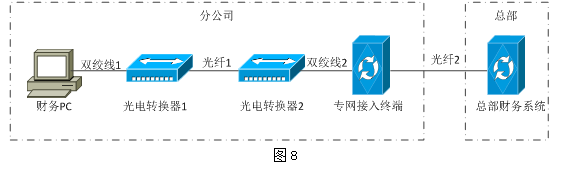
某分公司财务 PC 通过专网与总部财务系统连接,拓扑如图8所示。某天,财务PC访问总部财务系统速度缓慢、时断时好,网络管理员在财务PC端ping总部财务系统,发现有网络丢包,在光电转换器1处ping总部财务系统网络丢包症状同上,在专网接入终端处ping 总部财务系统,网络延时正常无丢包,光纤1两端测得光衰为-28dBm,光电转换器1和2指示灯绿色闪烁。 初步判断该故障原因可能是(作答此空),可采用( )措施较为合理。
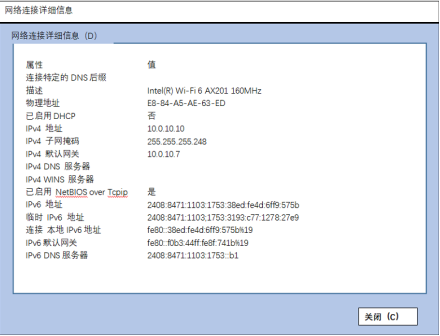
某主机可以ping 通本机地址,而无法ping通网关地址,网络配置如图7所示,造成该故障的原因可能是( )。
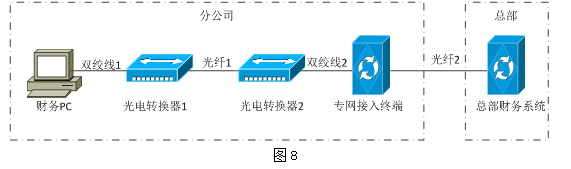
下列命令片段用于配置( )功能。